
Comprehensive Cybersecurity Solutions
Avenir Technologies provides Advanced Cybersecurity Solutions to protect your business from evolving threats. Our services include Network Security, Firewall Management, Endpoint Protection, Threat Detection, Data Encryption, and Compliance Solutions. With 24/7 Monitoring and Proactive Defense Strategies, we ensure Robust Security, Minimal Risks, and Uninterrupted Operations. Safeguard your digital assets with Avenir Technologies.
Cybersecurity Solutions – Protecting Your Business from Digital Threats
In today’s evolving digital landscape, cybersecurity is more critical than ever. At Avenir Technologies, we provide comprehensive cybersecurity solutions designed to protect your business from cyber threats, data breaches, and unauthorized access. Our proactive security approach ensures that your IT infrastructure, data, and applications remain secure, compliant, and resilient against modern cyber risks.
Network Security & Firewall Protection
Next-Gen Firewalls
Advanced firewalls with deep packet inspection, application control, and threat prevention.Intrusion Detection & Prevention Systems (IDS/IPS)
Proactively monitor and block malicious traffic before it reaches your critical systems.Secure VPN & Remote Access
Encrypted remote connectivity for your mobile workforce without compromising security.Zero Trust Network Architecture
Strict access controls and verification at every point of connection.Web & Content Filtering
Control access to web content and prevent phishing, malware, and data leaks.Threat Monitoring & Analytics
Real-time insights, alerts, and reporting for smarter security decisions.
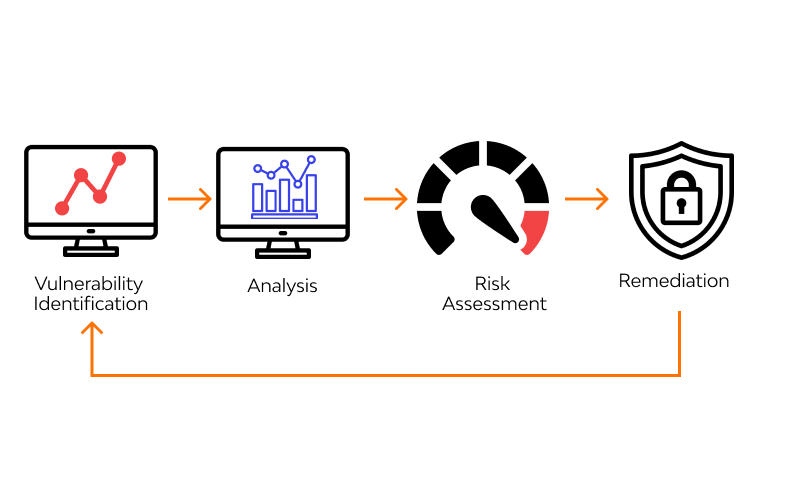
Threat Detection & Vulnerability Assessment
Vulnerability Scanning
Automated scans to detect weaknesses in networks, systems, and applications.Threat Intelligence Integration
Real-time data on emerging threats, malware patterns, and attack vectors.Penetration Testing
Simulated cyberattacks to test your defenses and identify exploitable vulnerabilities.Security Risk Assessments
Evaluate your entire IT landscape to uncover risks and prioritize remediation.Endpoint & Network Monitoring
Continuous threat detection across endpoints, servers, and connected devices.Detailed Reporting & Recommendations
Actionable insights with prioritized fixes and compliance alignment.
Identity & Access Management (IAM)
User Authentication & Single Sign-On (SSO)
Simplify access with secure, seamless login experiences across multiple systems.Role-Based Access Control (RBAC)
Enforce granular permissions based on job roles to minimize risk.Multi-Factor Authentication (MFA)
Add an extra layer of security with adaptive, easy-to-use verification methods.Identity Lifecycle Management
Automate onboarding, modifications, and offboarding of user accounts.Access Governance & Compliance
Monitor and audit access rights to meet regulatory standards like GDPR, HIPAA, and SOX.Integration with Cloud & On-Prem Systems
Unified identity management across hybrid environments for consistent security.

Data Encryption & Secure Cloud Solutions
Advanced Data Encryption
End-to-end encryption using industry-leading algorithms to protect data on-premises and in the cloud.Secure Cloud Architecture
Design and implementation of cloud environments with built-in security controls and isolation.Key Management Services
Robust encryption key generation, storage, and rotation policies for maximum security.Compliance & Regulatory Alignment
Solutions tailored to meet GDPR, HIPAA, PCI-DSS, and other data protection standards.Access Controls & Authentication
Integration of multi-factor authentication and identity management for secure cloud access.Continuous Security Monitoring
Real-time threat detection and incident response to protect your cloud assets.
Endpoint Security & Antivirus Protection
Next-Generation Antivirus (NGAV)
AI-driven protection against known and unknown malware.Endpoint Detection & Response (EDR)
Real-time analysis and rapid incident response for advanced threats.Patch & Vulnerability Management
Automated updates to keep your systems protected from security gaps.Remote Workforce Security
Enforce security policies and monitor devices outside your network.Centralized Management Dashboard
Unified control and visibility across all endpoints.


Security Information & Event Management (SIEM)
Real-Time Threat Detection
Identify suspicious activities and anomalies before they escalate.Log Collection & Correlation
Aggregate logs from servers, firewalls, endpoints, and cloud platforms to gain complete security insight.Automated Alerts & Incident Response
Quickly act on potential breaches with predefined response workflows.Compliance Reporting
Generate detailed reports to meet standards like GDPR, HIPAA, ISO 27001, and PCI-DSS.Security Analytics & Dashboards
Visualize threat trends and system performance through an intuitive interface.
Compliance & Regulatory Security
Compliance Gap Assessments
Identify vulnerabilities and areas of non-compliance across your systems.Security Policy & Framework Development
Implement robust policies aligned with standards like GDPR, HIPAA, ISO 27001, PCI-DSS, and more.Audit Readiness & Reporting
Prepare for audits with structured documentation and real-time compliance dashboards.Data Governance & Access Controls
Ensure sensitive data is accessed and managed securely across your organization.Continuous Compliance Monitoring
Automated tools to track and maintain compliance posture around the clock.

Incident Response & Disaster Recovery
Incident Response Planning & Execution
Rapid identification, containment, and eradication of threats with expert-led response teams.Disaster Recovery Solutions
Backup, replication, and restoration strategies to quickly recover critical systems and data.Root Cause Analysis & Forensics
In-depth investigations to identify vulnerabilities and prevent future attacks.Business Continuity Planning (BCP)
Tailored strategies to keep your operations running during and after a crisis.24/7 Monitoring & Support
Round-the-clock detection and mitigation to reduce response time and damage.
Why Choose Avenir Technologies for Cybersecurity?
- Proactive Threat Intelligence – Stay ahead of cyber threats with real-time monitoring and advanced AI-driven security solutions.
- Tailored Security Strategies – Our cybersecurity solutions are customized to fit your business size, industry, and risk profile.
- 24/7 Monitoring & Response – Our security experts work around the clock to detect and neutralize cyber threats.
- End-to-End Protection – From network security to data encryption and compliance, we cover every aspect of cybersecurity.
- Certified Security Experts– Our team holds industry-leading certifications in cybersecurity best practices.
At Avenir Technologies, we fortify your digital assets with cutting-edge cybersecurity solutions that provide unmatched protection, compliance, and peace of mind. Secure your business today and stay ahead of cyber threats!
Can we help you?

